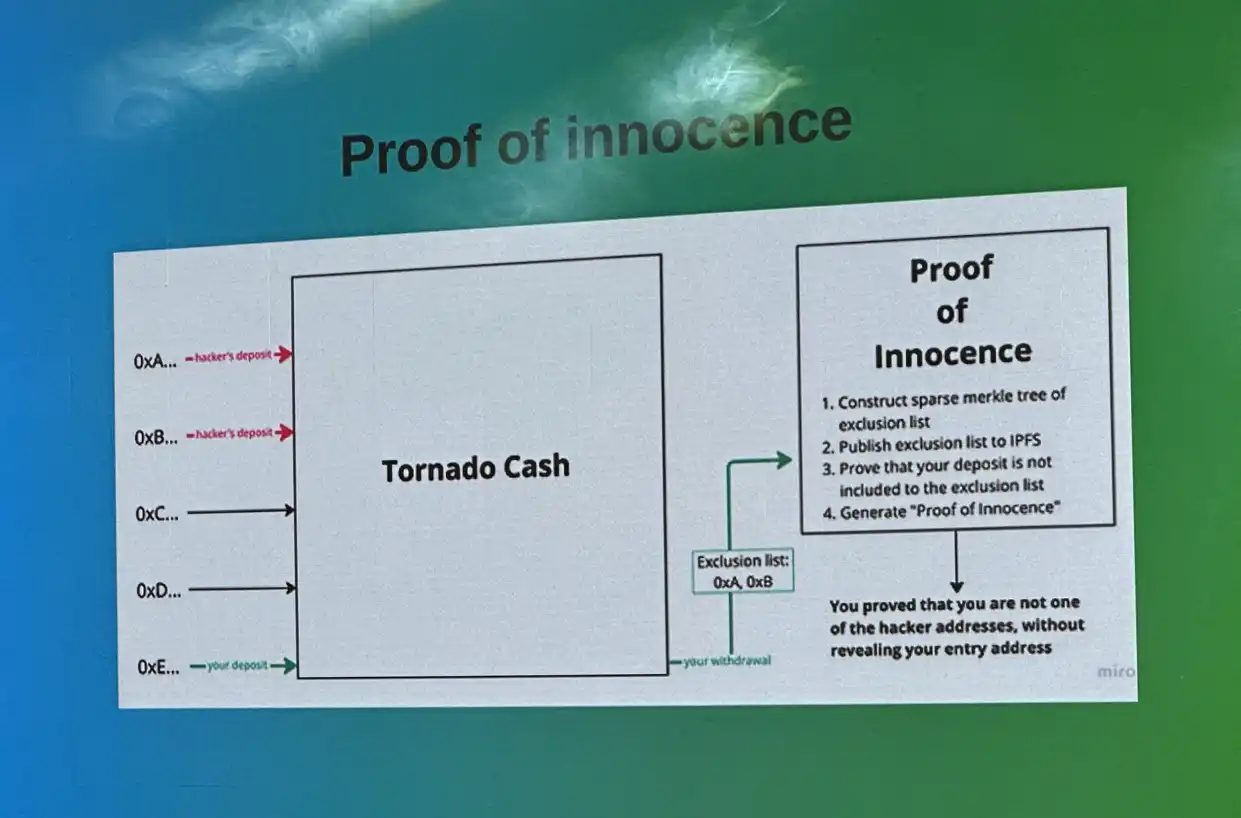
Let's talk about privacy. Based on the current context of blockchain technology, developing privacy technology would lead to a logical paradox. Would privacy ultimately become a wedding dress for hackers? However, if based on zk-SNARK, a Proof of Innocence (POI) scheme can be developed to ensure that users can enter and exit funds through privacy while avoiding the use of illegal elements for malicious purposes. Specifically, POI technology can be applied to protocols similar to Tornado.
POI technology provides each user with a digital fingerprint based on blockchain state history records and private key generation. When hackers attempt to launder money through Tornado's mixing transaction pool, if the withdrawal request address and deposit address provided by the hacker are contradictory (with different private keys), the transaction will be intercepted and returned to the original mixing address. This means that the hacker's unidentified assets cannot escape tracking through the mixing system.
Of course, as mentioned in V's speech, you can also directly build an exclusion list Merkle tree, which is equivalent to adding a blacklist mechanism to the Tornado protocol. Normal user deposits that are not on the list can generate innocent proofs and use Tornado normally, otherwise it is the opposite. Although blacklisting is effective, there is a centralization risk. Personally, I think it is more meaningful to block transactions where the input and output private keys do not match.
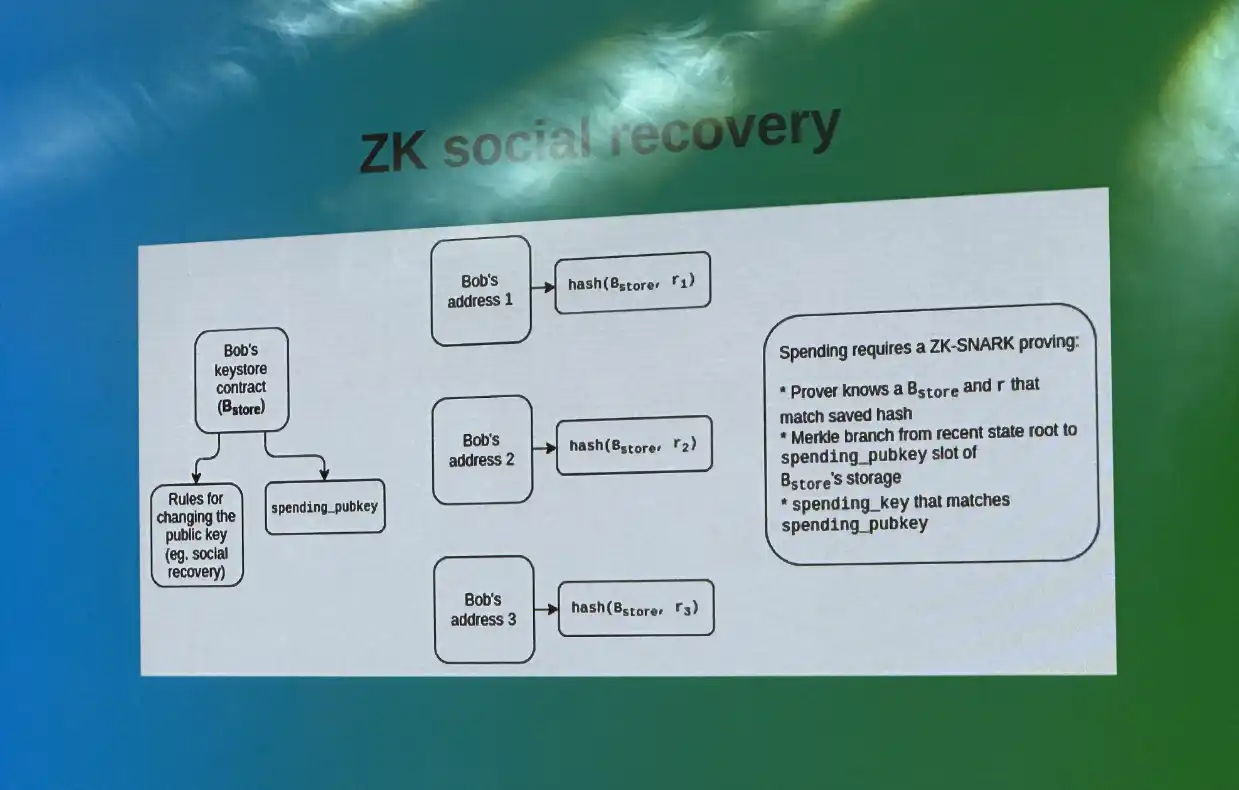
Lastly, let's talk about the security issue of third-party anti-censorship paradox. The Social Recovery feature is undoubtedly a path that blockchain must take for mass adoption. However, as we can see from the community protests that @Ledger faced when opening this feature, recovery cannot be based on the premise of centralization of third parties. The zk-SNARK technology can precisely solve this problem.
In simple terms, when a user generates multiple private key fragments, the fragments can be encrypted and zk-SNARK proof system can be used to generate proofs, which can then be distributed to trusted institutions or friends.
If the user loses their private key, they can request a third party to provide fragment data proofs, and then use zk-SNARK to verify the accuracy of these proofs, thereby achieving the function of social recovery without revealing private key fragments.
After fully understanding the above content, it is not difficult to see the importance of zk-SNARK technology for blockchain systems. It can solve various Ethereum network development paradox problems such as scalability and centralization, privacy and malfeasance, security and anti-censorship. Therefore, V God said that zk-SNARK will be as important as blockchain in 10 years, and maybe Ethereum will also be zk-SNARKized in the future. Well, zk-SNARKS Rule Everything Around Me.
Thank you @TommyDeng_DAO for summarizing the content of the Black Mountain V God Conference speech for the first time, as well as providing a large number of wonderful illustrations. The above technical thinking is only open thinking for reference, and everyone is welcome to discuss and criticize.
Original Link


 Forum
Forum Finance
Finance
 Specials
Specials
 On-chain Eco
On-chain Eco
 Entry
Entry
 Podcasts
Podcasts
 Activities
Activities
 OPRR
OPRR